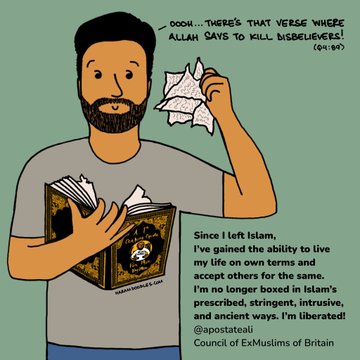
Ali Malik speaks to Maryam Namazie about the ex-Muslim movement, how it started, its aims and its impact on the human right to apostasy and blasphemy.
Category: Resources
By Hassan Radwan I’m frequently approached online by those who have lost their faith and a question that almost always crops up in various forms is: How do you cope without religion? For those of…
The hijab: “preventing common impositions” was published in Workers Liberty Solidarity in defence of banning child veiling on 27 November 2019. Maryam Namazie is an activist with the Council of Ex-Muslims and other secularist groups.…
‘Criticism of Islam or Islamism is not anti-Muslim bigotry’, The Freethinker, 15 July 2017
Our spokesperson, Maryam Namazie, was invited by Dabran Platform to speak at the Founding Congress of Enlightenment Feminism in Sulaymaniyah, Kurdistan (photos below). She spoke about Islam and Islamism as the greatest stumbling blocks for women’s…