With the official start of the new year (Nowroz) in Iran, the Iran Human Rights Organization has released a report on the executions carried out by the Islamic Republic. According to the report, the rate…
Category: Featured
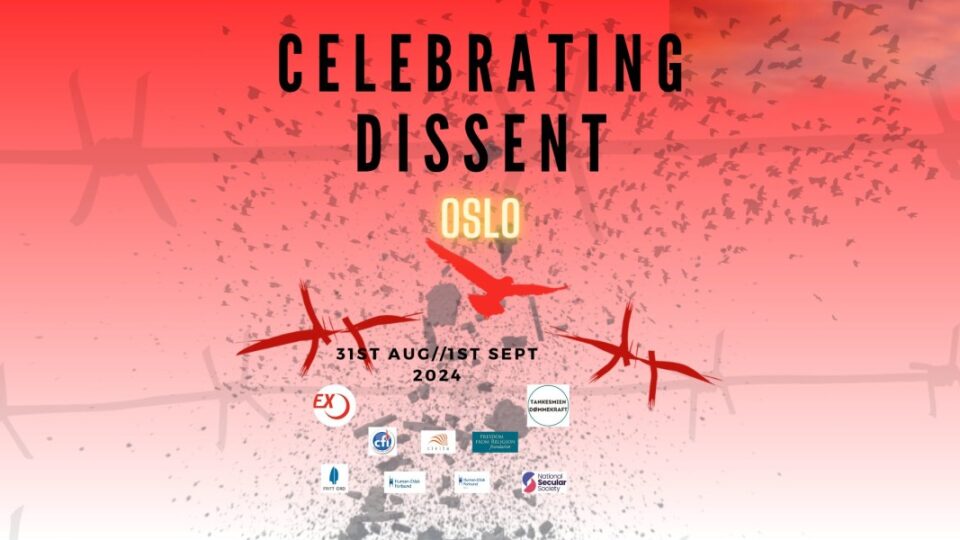
More than 50 freethinkers from Afghanistan, Algeria, Australia (including Cape Malay), Bangladesh, Canada, Croatia, Egypt, Germany, India, Iran, France, Kenya, Kosovo, Lebanon, Morocco, the Netherlands, Nigeria, Norway, Pakistan, Poland, Saudi Arabia, Somalia, Syria, Sweden, Switzerland,…
We were experiencing technical difficulties due to a change of servers. Everything is back up and working now But If you have gotten in touch with us in the last 2-3 weeks through any of…
CEMB organised fast-defying protests by staging picnics outside the embassies of countries that prosecute people for eating outdoors during the fasting hours of Ramadan. Fast-defying picnics were first started by feminist activist Ibtaissame Betty Lachgar…
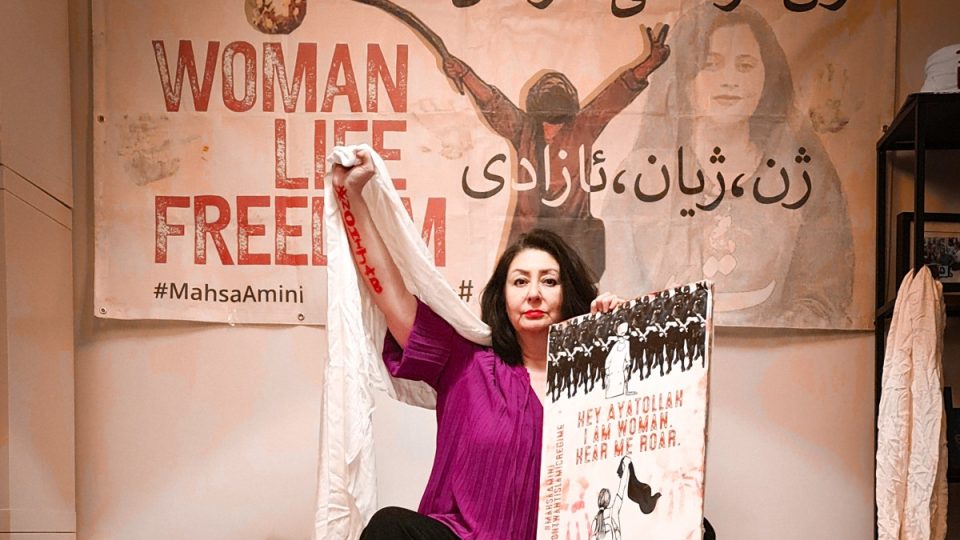
Today is #WorldHijabDay #veiledinstrength #unveiledinstrength #no2hijabday See World Hijab Day, uno strumento di repressione può diventare simbolo di orgoglio? Sky Italy, 1 February 2024 Fighting religious intolerance is important, as is fighting intolerance against those…